Blog
How Secure is the SAP Cloud?
December 5, 2022
December 5, 2022

There's no question that SAP Cloud is a powerful platform that can help businesses increase efficiency and productivity. However, as with any online system, security is a major concern. How vulnerable is SAP Cloud to hackers and other online threats? And what steps are being taken to ensure its security?
Here, we'll take a look at the security of SAP Cloud and how businesses can protect themselves against online attacks.
SAP Cloud security is a key concern for businesses considering cloud-based solutions, given the increasing importance of data protection and privacy in today's digital world. To ensure the safety and security of a business’s sensitive information and confidential data, several factors must be considered when selecting an SAP cloud solution.
SAP's data centers have undergone various certifications, such as ISO 27001, to ensure data safety and security. The physical security of these data centers is also important—they utilize state-of-the-art technologies to protect against unauthorized access, including multiple layers of authentication for users.
SAP's network and system protection solutions have been developed to preserve data integrity and access control. These solutions include tools such as firewalls, encryption protocols, intrusion detection systems, and vulnerability assessment software to help protect against malicious code or malware.
Compliance and data protection are other important areas that organizations must consider when evaluating SAP's cloud security solution. Data privacy laws require organizations to adhere to certain standards when it comes to the usage and storage of their customer's data. SAP is compliant with all relevant international regulations, including GDPR and HIPAA in Europe, J-SOX in Japan, etc., making them an ideal partner for businesses looking for a secure cloud solution.
Businesses should also look into the availability of recovery and backup processes provided by SAP, as well as the secure transfer of data. These measures help ensure that in the event of an outage or other issue, your business’s data can be quickly recovered with minimal disruption to operations.
SAP provides the most secure cloud-based systems available, with elaborate protection of networks and data centers, combined with regular penetration tests and a security monitoring center. The robust security features offered by SAP makes it an ideal choice for businesses looking to safeguard their mission-critical applications and data.
SAP systems are well-known for their tight security measures, which ensure the safety and integrity of data. SAP is a leader in enterprise technology, and its systems are used by some of the world's biggest companies to manage their operations. However, despite its impressive security record, there are still risks associated with managing an SAP system. While these risks can be avoided or mitigated through proper setup and maintenance of the system, it is important to understand exactly how SAP systems stay secure.
SAP systems use encryption technologies to protect data from unauthorized access both inside and outside the network. This ensures that sensitive information stored within a system is not accessible by anyone other than those who are authorized to access it. Additionally, SAP utilizes a suite of security tools that are designed to prevent the unauthorized use or modification of data within the system. These tools include user access management, application control, and audit trails that can be used to track and monitor any changes made to the system.
SAP also provides guidance on best practices for managing its systems safely and securely. This includes setting up roles and permissions for users, creating backup processes for recovering data in case of an emergency, and implementing stringent policies around user authentication within the system.
Authentication is a critical aspect of any secure network. With SAP Network, users must follow a multi-step authentication process before they are granted access to their accounts or other resources. This process usually involves entering a username and password, as well as answering security questions or providing further evidence of identities, such as fingerprint scans or facial recognition.
Next, once authenticated, all communications sent over the SAP Network are encrypted. This ensures that data is protected from malicious actors and kept confidential. Specifically, the network uses TLS (Transport Layer Security) 1.2, which is widely considered a robust encryption protocol capable of defending against man-in-the-middle attacks and other forms of eavesdropping.
In addition to encryption measures, SAP Network also employs various firewalls to limit access to certain areas of the network based on user permissions. These firewalls protect against unauthorized attempts to gain access or manipulate data, making it even more difficult for external threats to breach security.
Penetration testing is an important part of keeping cloud services secure. It involves running simulated attacks against a system to see how the system responds. The attack scenarios can range from simple ones, such as login attempts with known usernames and passwords, to more sophisticated ones that mimic advanced attacks in order to test every aspect of the system's security measures. Through these tests, any weaknesses in the security architecture can be identified before they become exploitable by malicious actors.
SAP's security monitoring center is responsible for monitoring the cloud environment 24/7 and responding quickly to any threats or vulnerabilities that are identified. The security team works with customers to ensure their data is protected, as well as evaluate new threats and implement solutions to mitigate them. SAP also provides customers with tools to help manage and monitor the security of their systems on an ongoing basis.
As you can see, there are several factors that come into play where security is concerned. These security protocols are all important to consider when entrusting your company’s critical data to any solution—particularly a cloud-based one.
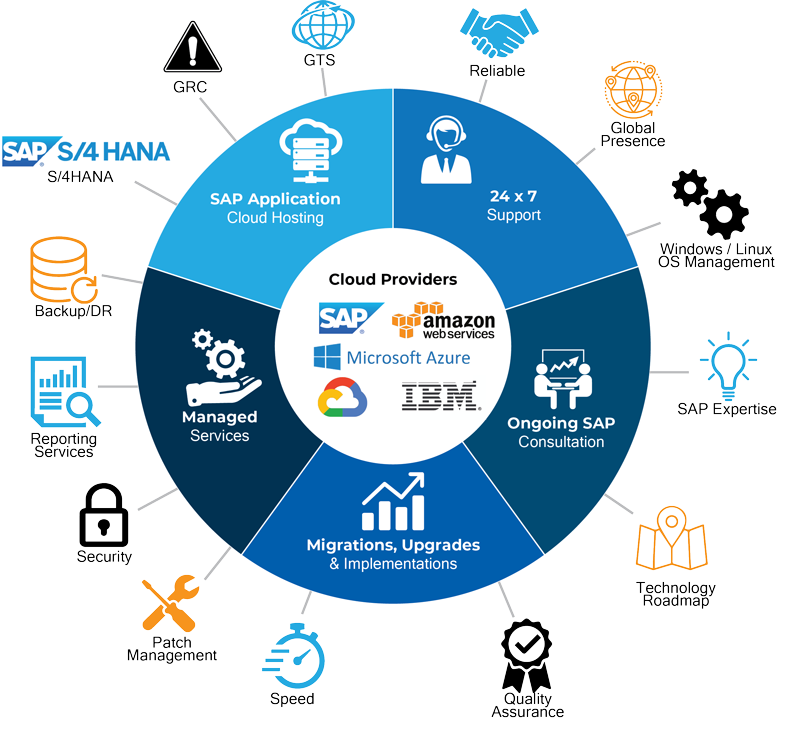
At Approyo, we specialize in finding the best solutions to meet your unique needs. Our experienced team is devoted to helping you get the most out of your SAP environment and keep it running smoothly. From organizing data efficiently and seamlessly integrating systems with existing platforms; to managing software deployments for maximum efficiency; to protecting critical data from unauthorized access — we have you covered.
Don’t leave your company’s valuable information vulnerable– contact Approyo today to learn how we can help you implement the perfect security solution for your business needs.

Approyo Security Team